Intel recommends the update to protect the processor
Researchers have found a vulnerability in some Intel processors that allows attackers to access encrypted data and install malicious firmware.

Researchers have found a vulnerability in some Intel processors that allows attackers to access encrypted data and install malicious firmware. When abused, the vulnerability opens the door to break through various chip security measures.
Intel is already aware of the problem and has advised affected users to download the latest firmware update to protect their systems.
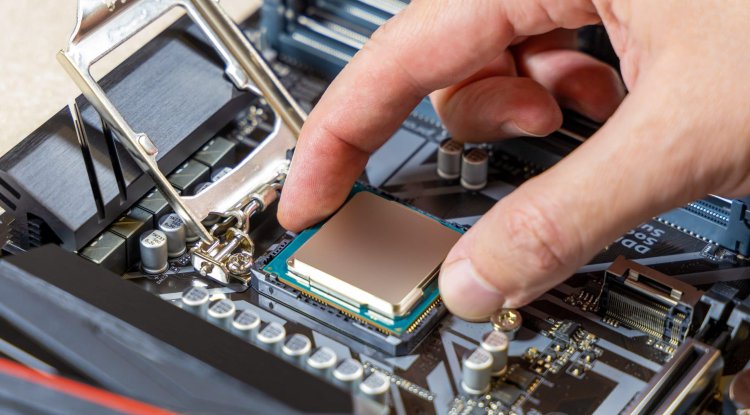
The vulnerability affects older Intel processors, including Intel Pentium, Celeron and Atom, which are based on the Gemini Lake, Gemini Lake Refresh and Apollo Lake platforms. Interestingly, it can only be used by hackers who physically own the chip - access only online will not compromise the processor.

Because of this security flaw, capable hackers who have the affected chip on hand are allowed to run it in debugging and testing modules commonly used only by firmware developers. This allows them to completely circumvent security measures, including Bitlocker and TPM protection, anti-copy blocks, and more, Digital Trends writes .
Programmer mode access allows an attacker to retrieve a data encryption key, which is typically stored in a TPM on Intel processors. TPM stands for Trusted Platform Module and is a microcontroller used to store keys, digital certificates, passwords and other sensitive data. If the TPM is used to protect the Bitlocker key, using the processor in developer mode also allows the attacker to break through that last wall of protection.
In addition to gaining access to sensitive data, a hacker could also break into the Intel Management Engine and run unauthorized firmware on the chip. The end result could be permanent access to the chip that could potentially remain undetected indefinitely. Security breach possible in a very short time
The whole process of gaining access to the processor and overcoming security measures takes only 10 minutes, which means that those with short access to the chip are able to potentially cause a huge security breach in a very short time.
Researchers Mark Ermolov, Dmitry Sklyarov, and Maxim Goryachy were the first to discover and report this vulnerability. They reported it to Intel and discussed the vulnerability, revealing further details of a possible breach. The Ars technique then reported the situation in more detail.
" We learned that you can get this key out of the safety locks. Basically, this key is encrypted, but we have also found a way to decrypt it and it allows us to execute arbitrary code within the control mechanism, extract Bitlocker / TPM keys, etc. , " Goryachy told Ars Technica.
This is not the first time that Intel products have been the target of various hacking attempts. In 2020, the same research team discovered a possible vulnerability that allowed attackers to decipher several Intel updates. There were also shortcomings in the Intel Boot Guard and Software Guard extensions.
Although Intel acknowledges that the latest vulnerability discovered is dangerous and has given it a high rating of severity, there have been no reports of users suffering from this security breach. Intel advises affected processor owners to simply install the latest firmware update to increase the security of their CPUs.