The Internet can track users by GPU fingerprint?
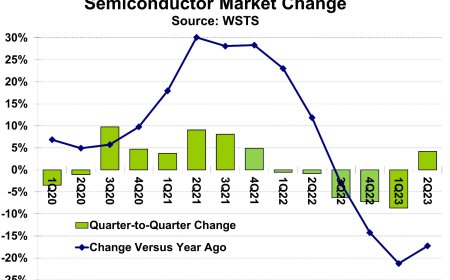
According to tests, the technology can help track users on the Internet by up to almost 67% longer.
- The DrawnApart technique allows you to run code to identify not a model, but a specific piece of graphics.
- The technology has the potential to be used to deliver customized ads online, allowing the user to follow up to almost 67% longer.
- Protection against surveillance in this way is difficult.
Research teams from the international academic community have demonstrated that Internet users can be tracked using the unique identifiers of their GPU, or graphics processing unit. The technique was dubbed DrawnApart (PDF), and it was tested on a total of 2,550 devices with 1,605 different graphics.
According to tests, the recognition of specific graphics works not only on computers but also on mobile devices and smartphones.
This method allows you to distinguish not only types and models but even specific pieces of graphics cards. This is caused by minor variations and tolerances in the manufacture of computer hardware.
These are, for example, characteristic imperfections of the selected production process, inaccuracies associated with mass production, or even random deviations.
In short, you can't get two completely identical computer chips on the market. Enthusiasts interested in overclocking, for example, know this - feel free to buy two processors with the same model designation, but you will not achieve the same performance when overclocking on them.
The same goes for graphics and other electronics.
A solution for customized ads?
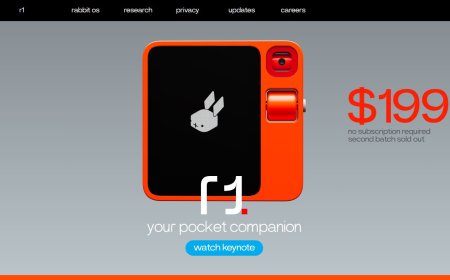
The researchers, therefore, investigated whether these differences at the hardware level could be detected and used in combination with the WebGL library. It is a very widespread and universal tool for programmers (API), thanks to which it is possible to work with 3D graphics directly in the browser.
The answer is that it works. When a website executes the required code, it can process unique graphics identifiers (GPUs) on the user's device as it is processed. If the user later visits the same page again, the site will recognize them based on the same identifier.
It works similarly when an ad placed on a website identifies the graphics card. An ad network that advertises on multiple sites can then track user behavior, including what sites they visit and what they're interested in.
In combination with other techniques, DrawnApart can extend a user's online tracking time by up to two-thirds. Instead of 18 days, it can take up to 30 days for a user's ad footprint to gradually disappear into a crowd.
The rest of the hardware has no effect
The whole DrawnApart technique basically works by giving the graphics a task when loading the page. Short GLSL programs with a predictable and standard way of processing are used. DrawnApart then monitors how the hardware handles the assignment and tracks, for example, the time it takes to process it.
Gradually, a unique digital fingerprint, an identifier of a specific graphic, will be created from 176 measurements and 16 different points. The researchers claim that the remaining hardware parts of the device have no effect on the measurement results. Likewise, the result is not affected by a load of other tabs opened in the browser or running applications in the background.
The devices, on the other hand, were kept in the operating temperature range of 26.4 to 37 ° C throughout the test, with no changes in supply voltage. This can be problematic for the practical application of the DrawnApart technique because the operating temperatures of the graphics can vary by tens of degrees Celsius depending on the load.
WebGL developers are already working on the study
As the Bleeping Computer website points out, there are only a few ways to defend against DrawnApart surveillance. Blocking scripts or selected APIs may help, but it seems more ordinary users can't do that. However, tracking would also be blocked at the API level if its developers added protection against this type of attack.
Finally, the non-profit organization Khronos, which develops the WebGL library, has already begun to study. It wants to explore potential solutions in response to researchers' findings. The topic of privacy is sensitive especially recently when there is growing pressure against tracking through cookies on the Internet.