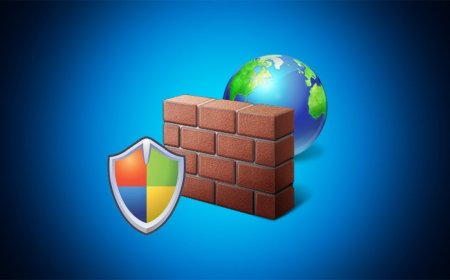
A gap in Java's Log4j causes a sensation

A critical zero-day vulnerability called Log4Shell in the widespread Java logging library Log4j endangers numerous servers and apps that can easily be hijacked and compromised by attackers.

The recently discovered Log4Shell vulnerability ( CVE-2021-44228 ) enables attackers to take over a vulnerable server or application with just one line of code by sending and processing manipulated requests. Since Log4j is a widespread part of the program, many well-known providers and services are also affected, such as Amazon, Apple's iCloud, Cloudflare, Steam, or Twitter.
The Federal Office for Information Security (BSI) has declared the highest warning level in the context of the vulnerability, while server administrators must counteract this with an update before attackers can locate the vulnerable systems and hijack them accordingly.
Otherwise, there is a threat of the attacker taking over the server and, in addition to data tapping, further attack scenarios such as extortionate ransomware or, in general, the distribution of malware or, for example, hidden crypto-mining software. Corresponding attacks have already been observed in some cases. Simple attack vector
With Log4Shell, a character string is entered in the log of the Java logging library, with the command to contact the directory service JNDI and to establish a connection to an LDAP server, which can then receive potentially malicious Java classes and execute them. Attackers only have to specify a server they control in order to hijack a server via logging.
A good example of the simple exploitation of the security gap is the popular video game Minecraft, where the game's chat function can be used to simply take over the entire game server with the appropriate character string. Remedy must be implemented
The version 2.0-beta9 to 2.14.1 of the always open source Log4j is affected by the security gap, whereby the Apache project released version 2.15.0 at short notice, which closes the gap. Accordingly, IT administrators are urged to secure their servers as quickly as possible. Linux distributions and Apache-based projects should now also deliver updated packages.
On the end-user side, there is nothing left to do other than to keep their own software up-to-date and to wait until all manufacturers patch their systems. After all, end-users are not directly in the focus of attackers using Log4Shell, but here too, vulnerable IoT devices in the smart home could make things critical. For example, network products, camera surveillance systems or digital locking systems, and automation technology that works with Java are also potentially at risk.