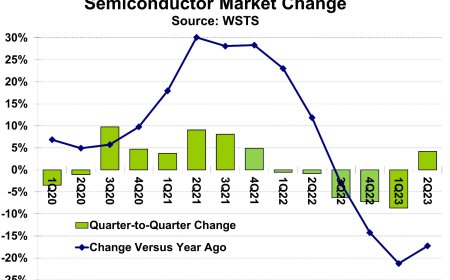
Cybersecurity for ICS experiencing special growth

In step with various estimates, within the period 2025-2026. This sector is going to be worth between 22.5 and 22.8 billion dollars, with an estimated CAGR rate of 5.81 percent to 7.2 percent. This is often a very important area for Serbia, because, in step with Kaspersky, the share of 39.4 percent of the overall number of those systems that were exposed to cyber attacks in November was the biggest globally.
Thanks to research and investigations of the growing number of attacks on industrial facilities and also the growing interest of the company and government sectors, the industry has already gathered a solid amount of data and offers for cover. However, it’s important to appear at how cybersecurity for ICS will still evolve and what challenges it’ll face in the future. Organizations can use this data to shape or tailor their security strategies today. The layering of operational technology protection
We need to seem at the present situation first. Protecting industrial infrastructure may be a complex task because it involves the employment of various tools for every level - from field devices and operations management to the boundaries of ICS systems and company IT systems. These are technologies for various industrial controllers, networks, computer protection and overall security management of enormous companies or perhaps holdings.
The primary task of ensuring the cybersecurity of any industrial organization and plant, like factories or substations, is to detect and take away threats at endpoints and networks in an exceedingly timely manner to shield the perimeter. The earlier a malicious object or activity is found, the less negative the impact of the attack.
If an industrial site has complex automation and control systems, it’s important to shield it from accidental breakdowns or intentional attacks. These are some samples of what these systems can be: automation of substations or power plants, discrete or continuous process automation, distributed or centralized control systems, field, monitoring or remote systems. The employment of dedicated tools to observe minor anomalies in performance indicators, as an example, the pressure indicator inside a tank for a petroleum refinery or powerhouse, to act before a malfunction occurs.
Organizing timely updates and vulnerability fixes in industrial firmware is essential to reducing the danger of cyber attacks. The fewer vulnerabilities within the equipment, the fewer potential gates that attackers can use to compromise the network. Unfortunately, it’s not always possible to detect and fix them by simply checking for updates from the vendor’s website. There should be a process for obtaining information from a reliable source about vulnerabilities, which provides the foremost complete information about the affected device and its configuration. With the help of this, decisive information is created on what to learn next, whether it is possible to use the right patch or if it is not possible to take measures of the current patch.
Last but not least, organizations need dedicated capabilities to detect threats and reply to advanced threats. Ideally, the ICS security system should collect and analyze all security events across the entire network in order that the interior security operations center or external expert service can identify signs of targeted attacks. This can help the corporate to prevent them in time and investigate the causes. This could work against advanced persistent threats to forestall them from lurking undetected within the network, as was the case with the Lazarus attack, which targeted the defense industry with a custom backdoor, as Kaspersky researchers recognized in 2020. Backdoor moved sideways through infected networks collecting sensitive information. This is where the difficulties begin
OT systems are getting more complex with their form of devices, remote connections and geographically distributed objects, and also the same is occurring with protection. Different tools, including but not limited to the above, work for various needs, some require integration, and each has its own dashboard. As a result, system-wide security management is becoming the foremost challenging task for businesses. Our global survey confirmed that two-thirds of business organizations consider the shortage of visibility in infrastructure and consistent security management to be the foremost difficult barriers against advanced threats (67 percent and 68 percent, respectively). Configuring each tool separately and manually managing everything will be a difficult task, inefficient, and ultimately can reduce the amount of protection. Different solutions don’t share threat information and there’s no visibility within the complete OT system. Bringing security to a typical denominator
Solving this problem means merging all parts of security into one point - an ecosystem that ought to offer users access to all or any possible solutions and services and adapt to the tasks of small, medium and enormous enterprises. It should offer one platform for managing all security tasks, including those from third-party services. In this way, all teams involved in OT security issues are going to be able to access the required data and processes.
An important function of the platform should be to observe and process security events from various sources, whether it’s an antimalware agent at endpoints, EDR, threat information, SIEM or the other tool, and to link them to events in IT networks. Data from various sources, analysis and exploration for correlations with the assistance of SOAR systems (Security Orchestration, Automation, and Response) will enable more efficient detection of complex targeted attacks.
A similar task already contains a cybersecurity solution for corporate IT. to confirm business data security and continuity, large companies want to boost the speed and efficiency of threat detection and research. The XDR approach - Extended Detection and Response - which mixes threat detection, research and response across all elements of the infrastructure is already gaining momentum in corporate IT security. The identical method will be adapted for OT security needs.
Such an ecosystem initiative will bring OT security to a more mature level. In step with Kaspersky’s vision, this may be the subsequent step within the evolution of OT security. this implies that organizations are going to be ready to protect their assets in a very more systematic way, better understand what’s happening in their networks and build a secure foundation for later digitization. The platform will enable the creation or strengthening of monitoring centers and can ensure industrial safety within large companies. In doing so, it may be used in several regions or maybe countries and trade unions, to empower national and international CERT organizations, moreover as external service providers (SMEs).