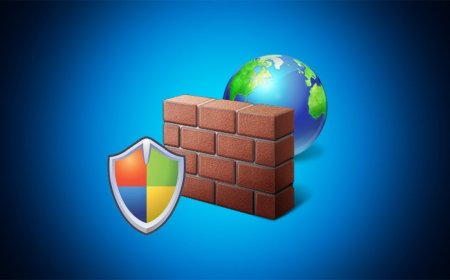
Half of the compromised instances of the Cloud have weak or no passwords
Cryptocurrency mining is the main malicious activity carried out by attackers after taking advantage of misconfigured instances hosted on GCP

Cryptocurrency mining is by far the main malicious activity carried out by attackers after taking advantage of misconfigured instances hosted on GCP, accounting for 86% of all post-compromise actions.
And in many cases, attackers move extremely fast after compromising the instance and installing cryptocurrency malware in order to free the CPU and GPU resources of others for free and thus make a profit.
"An analysis of systems used for unauthorized cryptocurrency mining, where timeline information was available, found that in 58% of situations, cryptocurrency mining software was downloaded into the system within 22 seconds of being compromised," Google said in a statement on the first Cloud Threat Intelligence report.

Another striking trend was how quickly attackers find and compromise unsecured instances facing the Internet. The shortest time to reach a compromise was 30 minutes after those instances were deployed. In 40% of cases, the time to reach compromise was less than eight hours. 80% of the 320 "honeypot" instances compromised within 24 hours
According to ZDNet, security firm Palo Alto Networks similarly found that 80% of the 320 "honeypot" instances located in the cloud - and designed to easily attract attackers - were compromised within 24 hours.
As the Google report points out, cryptocurrency malware is a problem for GCP users who do not take steps to protect their instances in the cloud.
" Although data theft does not appear to have been the target of these attacks, the risk remains of compromising funds in the cloud as attackers begin to commit multiple forms of abuse. "Public Internet-facing cloud instances were open to scanning and brute force attacks," Google notes.
GCP instances facing the Internet were a significant target of attackers. Slightly less than half of the compromised instances were carried by attackers who gained access to instances without a password or with a weak password for user accounts or API connections, which meant that these instances could be easily scanned.
" This suggests that the public IP address space is routinely scanned for vulnerable cloud instances. It will not be a question of whether a vulnerable Cloud instance will be detected, but when, " they said from Google.
In addition, 26% of compromised instances were due to vulnerabilities in third-party software used by the owner.
" Many successful attacks are the result of poor maintenance and a lack of basic control implementation, " summed up Bob Mehler, director of Google Cloud's CISO office.